Is your PC hacked? RAM Forensics with Volatility | Summary and Q&A

TL;DR
Learn how to analyze a heavily infected system using memory forensics tools like Volatility and identify malicious activities.
Key Insights
- 👻 Memory forensics allows analysts to uncover evidence of malware and compromised processes within a system's RAM.
- 🥟 Creating a memory dump is crucial for analyzing active programs and processes in memory.
- 🦻 Tools like Volatility, FTK Imager, and Intezer Analyze aid in memory forensics analysis.
- ❓ Memory injection and process hijacking are potential indicators of compromise.
- 🤨 Network forensics in memory analysis can help detect suspicious connections to external servers.
- ❓ Understanding the operating system is essential for distinguishing between legitimate and malicious processes.
- 👤 GUI tools like Volatility Workbench and Intezer Analyze provide user-friendly interfaces for memory analysis.
Transcript
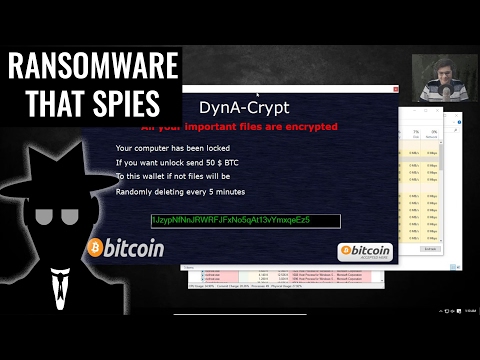
so how can you tell if a system is hacked in this video we're going to do a deep dive into memory forensics we're going to learn how to create a memory dump how to analyze it with tools like volatility we will look at Advanced command line tools and also very simple GUI tools that everyone can use what you're looking at right now is an infected sys... Read More
Questions & Answers
Q: What is the purpose of creating a memory dump in memory forensics?
Creating a memory dump allows forensic analysts to analyze the active programs and processes in a system's RAM, which may contain evidence of malicious activities or compromised processes.
Q: How can memory forensics help in identifying malware services?
Memory forensics enables analysts to identify malware services operating within a compromised system, helping to uncover hidden malicious activities and potential points of compromise.
Q: Why is an in-depth understanding of the operating system important in memory forensics?
Understanding the operating system allows forensic analysts to differentiate between legitimate system processes and potentially malicious processes, aiding in the identification and mitigation of security breaches.
Q: What are some tools recommended for memory forensics analysis?
Volatility is a widely-used open-source command-line tool for memory forensics analysis. For beginners, Volatility Workbench provides a user-friendly GUI interface. Other recommended tools include FTK Imager for capturing memory and Intezer Analyze for comprehensive system analysis.
Summary & Key Takeaways
-
The video focuses on conducting an in-depth analysis of a hacked system through memory forensics.
-
It demonstrates the process of creating a memory dump, analyzing it with tools like Volatility, and identifying malware and suspicious processes.
-
The video also suggests using tools like FTK Imager and Intezer Analyze for effective memory analysis.
Share This Summary 📚
Explore More Summaries from The PC Security Channel 📚